Chainalysis, a New York-based blockchain data platform that designs and develops anti-money laundering software for Bitcoin businesses, has published data under its 2022 Crypto Crime Report.
The report says that across all cryptocurrencies tracked by Chainalysis, total transaction volume grew to $15.8T in 2021, up 567 per cent from 2020’s totals. But considering the soaring adoption, it is also no surprise that cryptocurrencies are being used for illicit transactions by cybercriminals.
According to the data, over 4,068 criminal ‘whales’ hold over $25B in cryptocurrency from a multitude of illicit sources and represents 3.7 per cent of all cryptocurrency whales. In the crypto world, a whale is a private wallet holding over $1M worth of cryptocurrency. A criminal whale’s wallet has received more than 10 per cent of its funds from illicit addresses, according to Chainalysis.
All data discussed here is from the “Criminal Balances” section of the “Crypto Crime Report,” which analyses criminal activity on the blockchain from 2021 to early 2022.
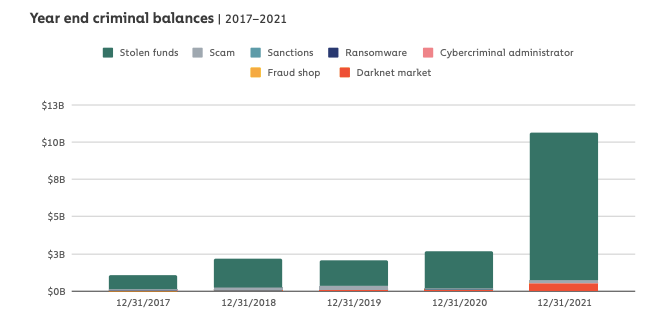
Year-end criminal balances
Chainalysis found out that there is a huge increase in criminal balances at the end of 2021. According to the report, criminals held $11B worth of funds with known illicit sources, compared to just $3B at the end of 2020.
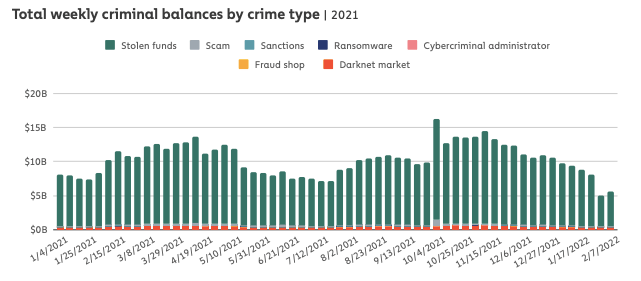
Stolen funds
The report reveals that at the end of 2021, stolen funds accounted for 93 per cent of all criminal balances at $9.8B. Darknet market funds are next at $448M, followed by scams at $192M, fraud shops at $66M, and ransomware at $30M.

Cryptocurrency holding time
According to the report, darknet market vendors and administrators tend to hold their funds the longest before liquidating, while wallets with stolen funds tend to hold for the shortest amount of time.
The data also shows holding times have decreased across the board, as the 2021 average holding times are at least 75 per cent shorter than the all-time figures in all categories.
Ransomware operators, in particular, now hold funds on average for just 65 days before liquidating.
“This may be a response to the mounting law enforcement pressure ransomware attackers face,” says the report.
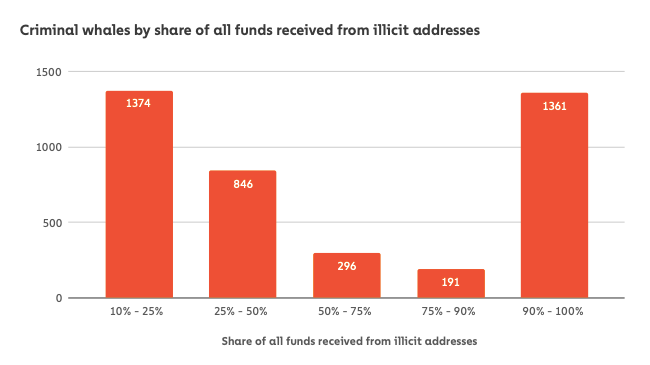
Criminal whales by share
The data shows that 1,374 criminal whales received between 10 per cent and 25 per cent of their total balance from illicit sources, while 1,361 had between 90 per cent and 100 per cent.
In total, 1,333 criminal whales received between 25 per cent and 90 per cent of all funds from illicit addresses.
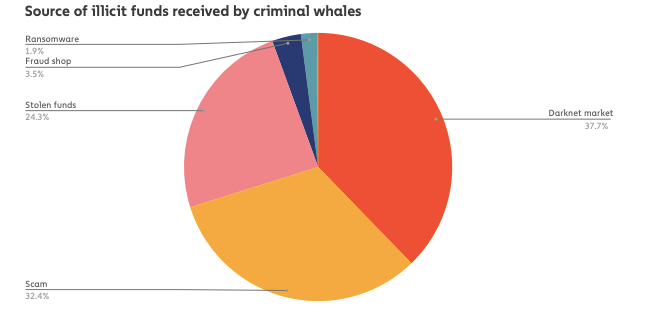
Illicit funds received by criminal whales also come from more varied sources than the funds making up overall criminal balances, adds the report.
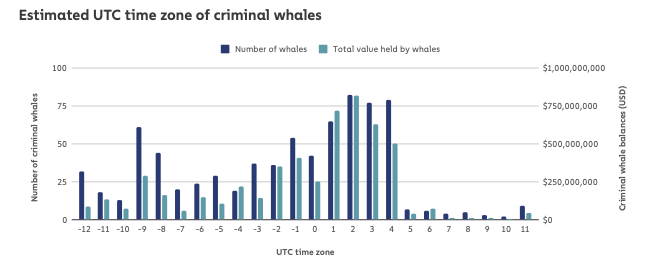
Estimated UTC time zone of criminal whales
UTC time zones 2, 3, and 4 are estimated to contain the most criminal whales, while time zones 1 and 9 also have a large number. UTC time zones 2, 3, and 4 include much of Russia, including major population centres like Moscow and Saint Petersburg.
All-time high
Cryptocurrency-based crime hit a new all-time high in 2021, with illicit addresses receiving $14B over the course of the year, up from $7.8B in 2020.
Crypto theft
Cryptocurrency theft grew even more, with roughly $3.2B worth of cryptocurrency stolen in 2021 — a 516 per cent increase when compared to 2020. Roughly $2.2B of those funds — 72 per cent of the 2021 total — were stolen from DeFi protocols.
In 2020, just under $162M worth of cryptocurrency was stolen from DeFi platforms, which was 31 per cent of the year’s total amount stolen. In 2021, that figure rose to another 1,330 per cent. Also, DeFi protocols saw the most growth by far in usage for money laundering at 1,964 per cent.
Fight against cryptocurrency-related crime
In November 2021, for instance, the Internal Revenue Service (IRS) Criminal Investigations division of the US announced that it has seized over $3.5B worth of cryptocurrency in 2021 — all from non-tax investigations — representing 93 per cent of all funds seized by the division during that time period.
“We’ve also seen several examples of successful seizures by other agencies, including $56 million seized by the Department of Justice in a cryptocurrency scam investigation, $2.3 million seized from the ransomware group behind the Colonial Pipeline attack, and an undisclosed amount seized by Israel’s National Bureau for Counter Terror Financing in a case related to terrorism financing,” says the report.